[Intelink-U copy of this post]
I work in the Office of the DoD CIO. For more than 10 years, “Net-Centricity” was the buzzword that we hung our hats on. This is the sort of trick that policy wonks like me use: we make up a term, and try to get everyone else to buy into it. To understand what the term means, you have to adopt a little piece of our worldview. Even if you don’t agree with the idea, you still have to buy into it a little, just to be able to converse with us. “Net-Centricity” was such a term. It meant whatever we wanted it to mean. We belittled people for doing things that weren’t “net-centric”, without explaining what we meant in English. Ah, the good old days.
Even the true believers could disagree vehemently about whether something was “net-centric”, or net-centric enough. And I was definitely a true believer. Maybe I still am.
Sadly, perhaps, the term is falling out of vogue. We promised too much; eventually the people we were trying to convince became disillusioned. We actually accomplished a lot, but now it’s fashionable to belittle “net-centricity” in favor of the next-big-thing. (At the moment, that appears to be “data-centricity” – (but it means the same thing).
Now that the term is deprecated, I can finally tell you what it means. Are you ready? There is a fundamental theory and a fundamental premise. Here is what “net-centric” means:
THE FUNDAMENTAL THEORY OF NET-CENTRICITY
“Better information leads to better decisions, which in turn, leads to better outcomes.”
This, I emphasize, is only a theory. It is easy to point out situations where it is wrong. For example, there is a well-documented phenomenon sometimes called “analysis paralysis”, wherein a decision maker becomes so accustomed to getting new information that he becomes incapable of making a timely decision, preferring to wait for more data. Another weakness in the theory is the definition of “better”. What does “better” mean, in the context of information, decisions, or outcomes?
In general though, it’s a pretty good theory and even verges on being tautological. Consider, for a moment, that the word “information” simply means “a fact which informs a decision”.
All the ideas of net-centricity are rooted in this theory, combined with practical observations about information technology, which helps us get that information when we need it.
THE FUNDAMENTAL PREMISE OF NET-CENTRICITY
Taking best-practices and design patterns from the development of the Internet, and applying them to defense problems helps decision makers to make better informed decisions.
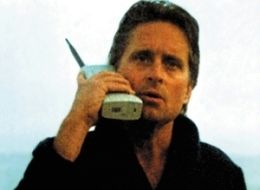
The existence of a ubiquitous computer network (The Internet) has changed the way we shop, the way we travel, the way we meet people, the way we do research, the way we bank, the way we invest, the way we communicate, the way we raise money, the way we goof-off, and the way we vote. It is just barely beginning to change the way we fight wars and defend our nation.
Net-centricity was just a buzzword in the Defense Department that meant, “Why can’t we be more like the Internet?” Now you know the secret.
Part of the shift away from the term “net-centricity” is based on the absolutely true observation that it’s the data, the information, that really matters. The net is just the technology that gets the information to us. In DoD, it became easy to get distracted by “wireheads”, people who were only interested in building networks. Wireheads fall into two camps: ones who don’t understand Metcalfe’s law (the value of a telecommunications network is proportional to the square of the number of connected users of the system), and are constantly trying to build new networks to get systems to talk to each other, and ones who do understand Metcalfe’s law and are therefore trying to eliminate redundant networks by connecting them into the master fabric.
The focus on networking technology was unfortunate. The visionaries who really understood net-centricity: John Stenbit, Priscilla Guthrie, Dave Alberts, (and many others) never made this mistake. For a year or two, there was a ridiculous internal debate about the difference between “network-centric” and “net-centric”. Folks would make the distinction that “network-centric” was about networking technology, but “net-centric” was about the data on the network. (I personally observed at the time that ‘net’ was either shorthand for ‘network’ or it was a piece of fishing equipment, and the whole conversation was stupid, IMHO.)
At the end of the day, the internet does a lot of things right that we still don’t really understand inside government. As just one example, on the internet, people go out of their way to make stuff discoverable. There’s a whole career field called “Search Engine Optimization”. In government, sadly, we still keep our information on the “H:” drive (or whatever), and the idea that someone else might want to see our data is often seen as abhorrent.
It’s 2013 and I proclaim: “net-centricity” is dead; Long live “data centricity”! Or the “Joint Information Environment”. Or whatever. Out with the old buzzwords, in with the new! And do it in the Cloud with Social Media! Oh, and Digital Government!
Hopefully some of the good ideas will still be there with new hats.
 [This is mirrored on Intelink-U]
[This is mirrored on Intelink-U]